Exploring Quantstamp Crypto Innovations in Blockchain Audits

Navigating the Landscape of Quantstamp Crypto
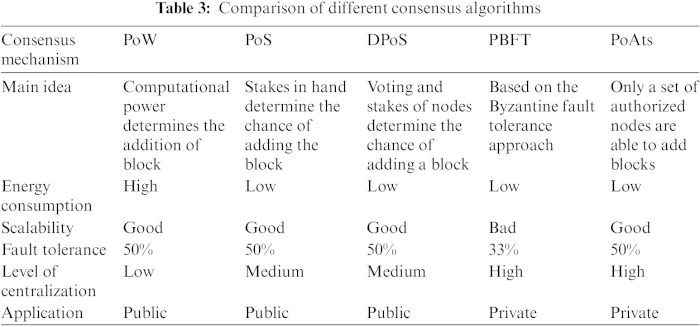
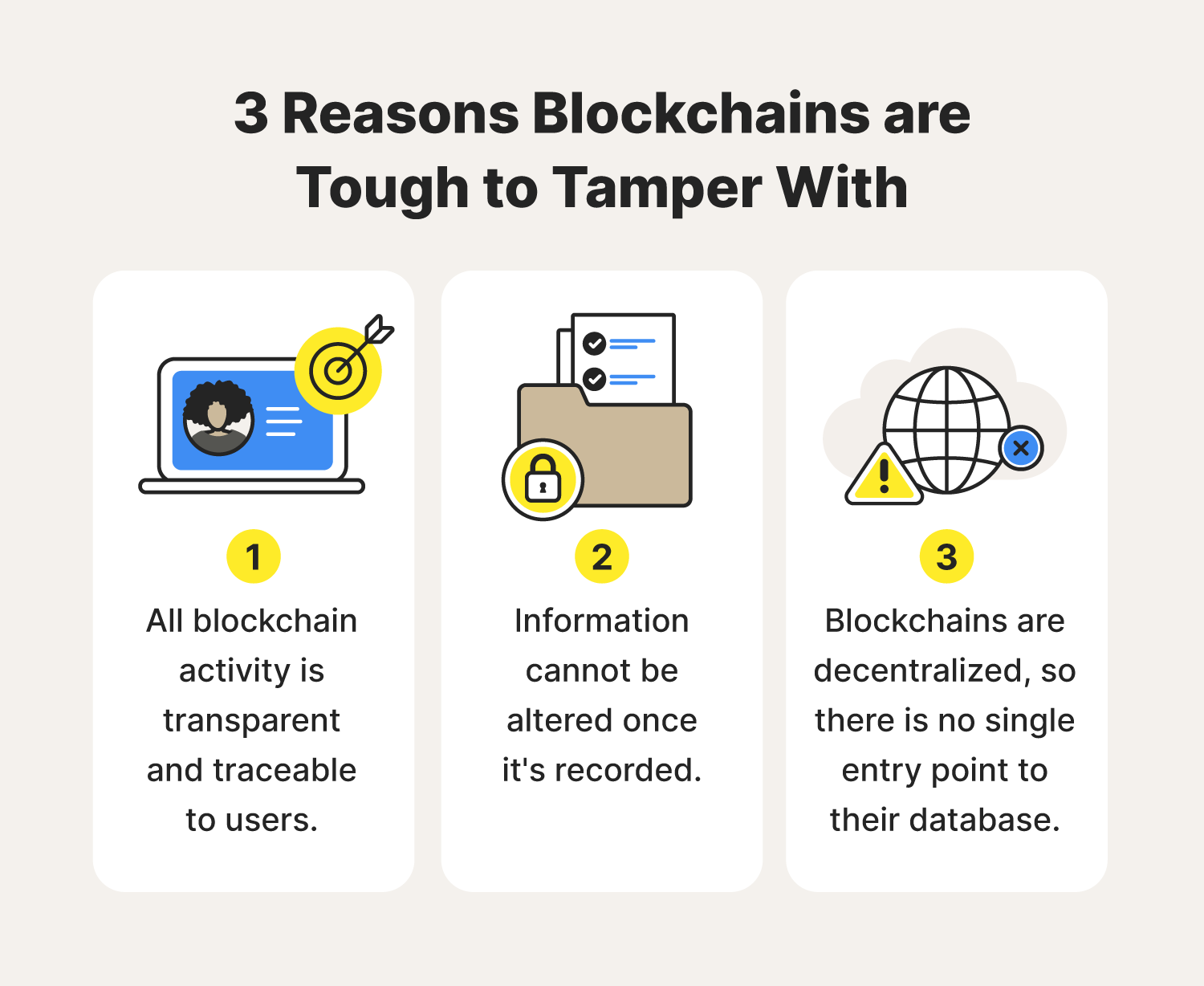
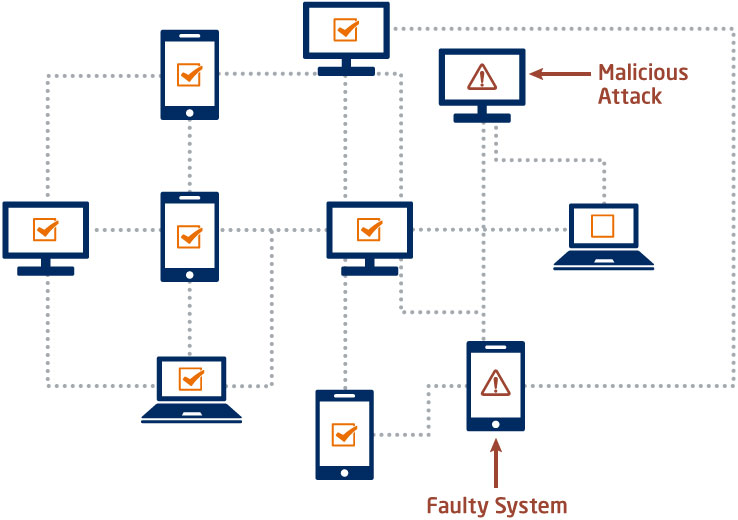
Understanding Blockchain Security
In the fast-paced world of cryptocurrency, security is paramount. With the rise of blockchain technology, ensuring the integrity and safety of digital assets has become more critical than ever. Enter Quantstamp Crypto – a pioneering solution designed to address the security challenges inherent in decentralized finance.
The Role of Quantstamp Crypto
At its core, Quantstamp Crypto serves as a guardian of blockchain integrity, offering advanced security audits and solutions to safeguard digital assets. By leveraging cutting-edge technology and expertise, Quantstamp Crypto aims to fortify the foundation of decentralized finance, instilling confidence and trust among investors and developers alike.
Innovative Security Audits
Quantstamp Crypto employs a comprehensive approach to security audits, meticulously examining smart contracts and blockchain protocols for vulnerabilities and weaknesses. Through a combination of automated scanning tools and manual code reviews, Quantstamp Crypto ensures that digital assets remain protected from potential threats and exploits.
Building Trust in Decentralized Finance
In the rapidly evolving landscape of decentralized finance, trust is paramount. Quantstamp Crypto plays a crucial role in building trust among investors and users by providing transparent and reliable security assessments. By identifying and mitigating risks, Quantstamp Crypto helps foster a safer and more secure environment for financial transactions on the blockchain.
Empowering Developers with Confidence
For blockchain developers, ensuring the security of smart contracts and protocols is essential. Quantstamp Crypto empowers developers with the confidence to deploy their creations on the blockchain by offering comprehensive security audits and recommendations. By partnering with Quantstamp Crypto, developers can rest assured that their projects are built on a foundation of trust and reliability.
Addressing Security Challenges
Despite the numerous benefits of blockchain technology, security remains a significant concern. Quantstamp Crypto addresses these challenges head-on by providing proactive security solutions and audits tailored to the unique needs of decentralized finance. By staying ahead of emerging threats and vulnerabilities, Quantstamp Crypto helps mitigate risks and protect digital assets.
Setting the Standard for Security
In the ever-evolving landscape of cryptocurrency, standards for security are continually evolving. Quantstamp Crypto sets the standard for security audits and solutions, leveraging its expertise and experience to stay at the forefront of blockchain security. By continuously refining its methodologies and tools, Quantstamp Crypto remains a trusted partner for ensuring the integrity of digital assets.
Embracing Innovation
As blockchain technology continues to evolve, so too does Quantstamp Crypto. By embracing innovation and staying ahead of emerging trends, Quantstamp Crypto remains at the forefront of blockchain security. Whether it’s adopting new technologies or expanding its suite of services, Quantstamp Crypto is committed to driving the future of decentralized finance forward.
Collaborating for a Secure Future
In the collaborative world of cryptocurrency, partnerships are essential. Quantstamp Crypto collaborates with industry leaders, developers, and stakeholders to ensure a secure and resilient blockchain ecosystem. By working together, we can address security challenges more effectively and build a future where digital assets are protected and accessible to all.
Conclusion
In conclusion, Quantstamp Crypto plays a pivotal role in ensuring the security and integrity of blockchain technology. Through innovative solutions, proactive security audits, and collaborative partnerships, Quantstamp Crypto is shaping the future of decentralized finance, fostering trust and confidence among investors, developers, and users alike. Read more about quantstamp crypto