Cryptographic Hash Functions: Ensuring Digital Security

Safeguarding Digital Integrity: The Role of Cryptographic Hash Functions
Cryptographic hash functions stand as the guardians of digital security, providing a robust layer of protection for data integrity and authentication. In this exploration, we delve into the world of cryptographic hash functions, understanding their significance, applications, and the principles that make them essential in the realm of cybersecurity.
What are Cryptographic Hash Functions?
At their core, cryptographic hash functions are algorithms that take input data and produce a fixed-size string of characters, often referred to as the hash or hash value. The critical property of these functions is that even a small change in the input data results in a significantly different hash. This one-way function ensures that it is computationally infeasible to reverse the process and retrieve the original data from its hash.
Ensuring Data Integrity
One of the primary applications of cryptographic hash functions is in ensuring the integrity of data. When data is hashed, the resulting hash value is like a unique fingerprint for that specific set of information. Any alteration, no matter how minor, in the input data would lead to a completely different hash value. By comparing the computed hash with the original hash, users can quickly identify whether the data has been tampered with.
Password Hashing: Protecting User Credentials
Cryptographic hash functions play a pivotal role in securing user credentials. Instead of storing actual passwords, systems store the hash values of passwords. During authentication, the entered password is hashed and compared to the stored hash. Even if a database is compromised, attackers would only gain access to hashed values, which are computationally challenging to reverse into the original passwords.
Digital Signatures: Verifying Authenticity
Digital signatures leverage cryptographic hash functions to ensure the authenticity and integrity of digital messages or documents. When a user signs a document, the hash of the document is encrypted with their private key, creating a digital signature. Anyone with access to the signer’s public key can verify the signature by decrypting the hash, confirming both the origin and integrity of the document.
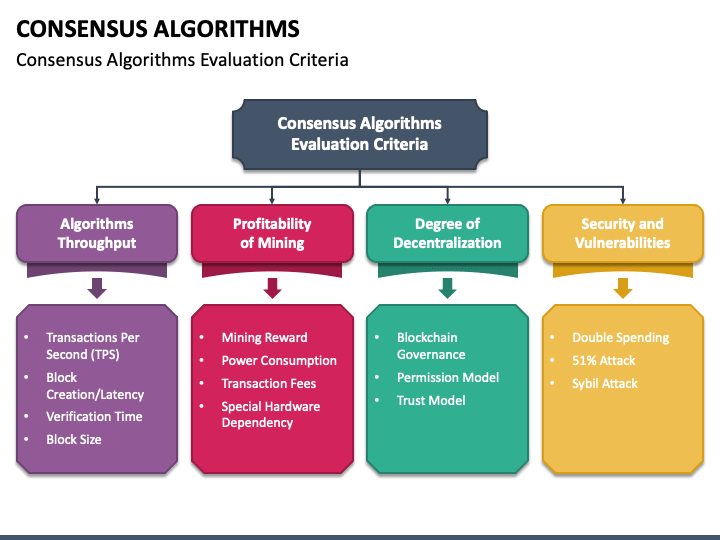
Blockchain Technology: The Backbone of Security
Cryptographic hash functions form the backbone of blockchain technology. Each block in a blockchain contains a hash of the previous block, creating a chain that links all blocks together. This chaining, combined with the one-way nature of hash functions, ensures the immutability of the entire blockchain. Altering any block would require changing all subsequent blocks, an infeasible task due to the computational effort involved.
Avalanche Effect: The Power of Unpredictability
The avalanche effect is a crucial characteristic of cryptographic hash functions. A small change in the input should lead to a drastically different output. This inherent unpredictability ensures that even a minor modification in the original data results in a completely different hash value, enhancing the security and reliability of cryptographic applications.
Real-world Implementation: Cryptographic Hash Functions in Action
Explore Cryptographic Hash Functions for insights into real-world examples and practical applications. This platform offers a closer look at how cryptographic hash functions contribute to data security, integrity, and authentication across various domains.
Considerations and Best Practices
While cryptographic hash functions provide robust security, certain considerations and best practices are essential. Using well-established algorithms, incorporating salt values in password hashing, and regularly updating cryptographic protocols are crucial steps in maintaining the effectiveness of hash functions against evolving security threats.
Future Developments and Challenges
As technology advances, the field of cryptography evolves. Ongoing research aims to develop new cryptographic hash functions that resist emerging threats, such as quantum computing. Addressing potential vulnerabilities and staying ahead of malicious actors will be essential in ensuring the continued effectiveness of cryptographic hash functions in the digital age.
Conclusion: Guardians of Digital Trust
In conclusion, cryptographic hash functions serve as the guardians of digital trust, underpinning the security of countless applications in the digital realm. From data integrity to password protection and blockchain immutability, the versatile applications of hash functions make them indispensable in the ongoing battle for cybersecurity. As technology progresses, the role of cryptographic hash functions will only grow in significance, shaping the future of secure digital communication and data management.