Ensuring Robust Smart Contracts: A Guide to Security Best Practices
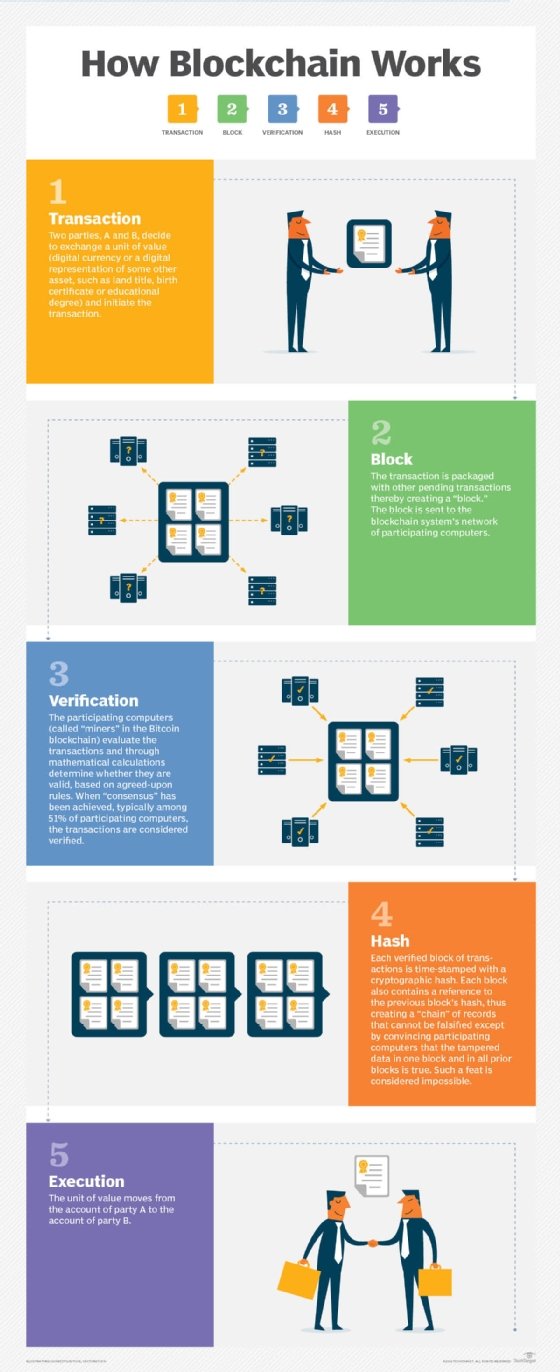
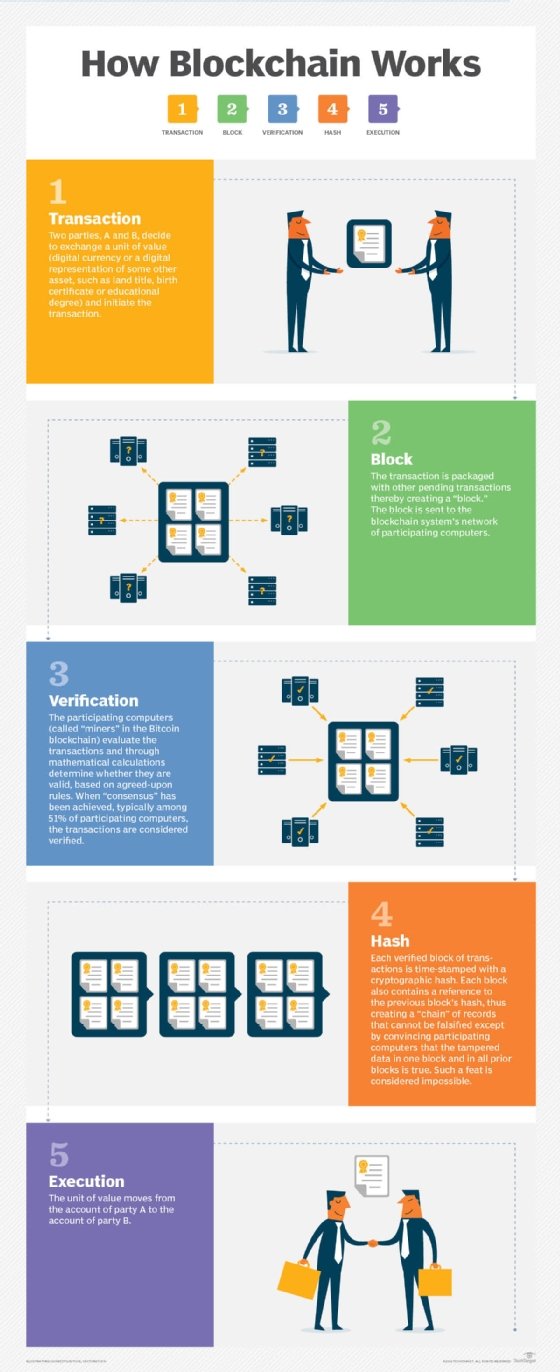
Smart contracts, integral to blockchain functionality, require meticulous attention to security. This article explores essential best practices for smart contract security, emphasizing the importance of proactive measures to mitigate vulnerabilities and safeguard decentralized applications.
Code Auditing and Review
A fundamental step in smart contract development is a thorough code audit and review. Engage experienced blockchain developers and auditors to scrutinize the code for vulnerabilities, bugs, and potential exploits. Regular audits, especially before deployment, help identify and rectify security issues in the early stages of development.
Use of Established Libraries and Standards
Leveraging well-established libraries and adhering to established standards contribute significantly to smart contract security. Utilizing widely accepted frameworks and libraries reduces the likelihood of coding errors and ensures compatibility with existing blockchain ecosystems. Following established standards enhances interoperability and compliance with best practices.
Limiting Contract Permissions
Implement the principle of least privilege by restricting the permissions of smart contracts to the bare minimum necessary for their intended functionality. By limiting access to critical functions and sensitive data, developers reduce the attack surface and minimize the potential impact of security breaches.
Properly Handling External Calls
Smart contracts often interact with external contracts or oracles. Ensuring secure handling of external calls is crucial to prevent malicious actors from manipulating the contract’s behavior. Implement checks and validations to verify the authenticity and integrity of data received from external sources.
Secure Data Handling
Protecting sensitive data within smart contracts is paramount. Utilize encryption techniques to secure confidential information and avoid storing excessive data on the blockchain. Minimizing on-chain storage not only improves efficiency but also reduces the exposure of sensitive data to potential attackers.
Continuous Monitoring and Upgrades
Security is an ongoing process. Implement continuous monitoring mechanisms to detect and respond promptly to any suspicious activities. Additionally, be prepared to deploy upgrades when vulnerabilities are identified or when improvements can be made to enhance the overall security posture of the smart contract.
Addressing Reentrancy Vulnerabilities
Reentrancy vulnerabilities pose a significant threat to smart contracts. Employ best practices to prevent reentrancy attacks, such as using the Checks-Effects-Interactions pattern, where state changes occur before interacting with external contracts. This pattern minimizes the risk of reentrancy exploits.
Contract Decomposition
Breaking down complex smart contracts into smaller, modular components known as contract decomposition enhances security. Smaller contracts are easier to audit, test, and maintain. This approach facilitates focused attention on individual components, reducing the likelihood of overlooking vulnerabilities.
Community Engagement and Disclosure Policies
Establishing open communication channels with the developer community and users is crucial for smart contract security. Encourage responsible disclosure of vulnerabilities and promptly address reported issues. Having clear disclosure policies fosters a collaborative and security-focused ecosystem.
Educating Stakeholders
The human factor plays a significant role in smart contract security. Educate developers, users, and other stakeholders about security best practices, potential risks, and common attack vectors. A well-informed community contributes to the overall security posture and reduces the likelihood of unintentional security lapses.
Real-world Implementation: Smart Contract Security Best Practices
Explore Smart Contract Security Best Practices for practical insights, case studies, and examples illustrating the effective implementation of security measures. This platform offers valuable resources to developers and stakeholders aiming to enhance the security of their smart contracts.
Conclusion: A Secure Future for Smart Contracts
In conclusion, prioritizing security in smart contract development is imperative for the sustained growth and adoption of blockchain technology. By adhering to these best practices, developers can fortify smart contracts against potential threats, contributing to a more secure and resilient decentralized ecosystem. As the landscape evolves, continuous improvement and collaboration will be key in ensuring the longevity and trustworthiness of smart contract applications.